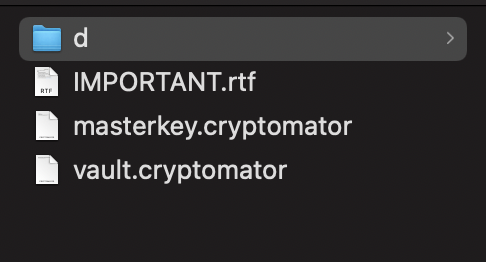
You can delete the „important.rtf“ file as this contains only information you should read. If you have read it, feel free to delete it.
Do not delete any of the other files in your root.
These files are necessary to decrypt your files. If you delete them, all your files in the vault are lost.
What about masterkey.cryptomator.xxxxxx.bkup and vault.cryptomator.xxxxxx.bkup (where xxxxxx is some random-looking string), Those look like backups, made before we changed our password or vault structure. Is it ok to delete those? (being very careful to delete only the *.bkup files, and nothing else). I was under the impression it might be a good idea to get rid of the older maskerkey backups since those preserve ways to decode the keys using older passwords. I haven’t deleted anything yet because I’m not positive… just wanted to double check.
Thats not quite right. (see here)
But you are right, these are backups just in case something really bad happens with your masterkey files. You can delete them if you have backups else where.
Thanks Michael.
I backup my entire vault directory periodically with no special attention to the masterkey.cryptomator and similar files (I have a small vault).
I see here it says “The .bkup file is a backup of your masterkey file. It’s created after every successful unlock.”
My vault directory includes several older masterkey.cryptomator.xxxxxx.bkup files including prior to my last password change. To my thinking, they represent a vulnerability to accessing the vault using the older password (which had less entropy). I realize there may also be cloud copies of older versions of those masterkey and backup files, but I’d still rather not have those older versions stored right there with the data if they are not serving any useful purpose.
To me, the logical approach would be delete all but the most recent (by timestamp) .bkup file since the older ones don’t add any value as long as I have the most recent .bkup. Does that sound reasonable to you?
Please read my linked post what exactly happens when you change your password. Then you’ll see that the masterkey file (after a password change) is not more or less secure.
Changing the password does not change the encryption itself. Therefore, changing the password does not mean that every file hast to be again encrypted.
In your link, overheadhunter said “The actual files will not get re-encrypted, meaning you can not upgrade a weak passphrase to a stronger one once the data has been synced to a service that allows recovery of older versions of the masterkey file.”
The vulnerability lies in the older versions of the masterkey file. Those might exist with the cloud provider, but they also exist in the bkup files, don’t they?
Sorry, I did get you wrong. I thought you are trying to „stronger“ the encryption itself.
So yes, if you changed your weak password then it’s reasonable to delete the according backup masterkey files as well. But do your self a favour and keep the some where else, at least a while. Just in case. 
Thanks. Here’s what I did
- Made a complete backup of my vault
- Deleted all but the most recent masterkey.cryptomator.bkup.
- opened vault, closed vault, checked for new bkup… none was there.
- Deleted the last remaining masterkey.cryptomator.bkup (which I had backed up elsewhere anyay).
- opened vault, closed vault, checked for new bkup… indeed a new bkup was there.
So I think cryptomator produces a masterkey.cryptomator.bkup when the vault is accessed, PROVIDED that one of two conditions is met:
- Password was changed.
-
OR - It can’t find any other masterkey.cryptomator.bkup file in the vault.
That sort of makes sense, there’s no need for it to create .bkup file if it finds that there is already a current one there.