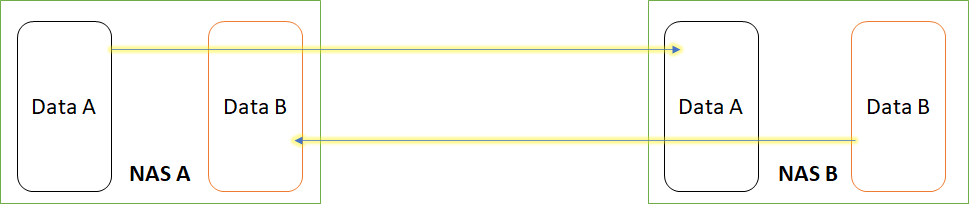
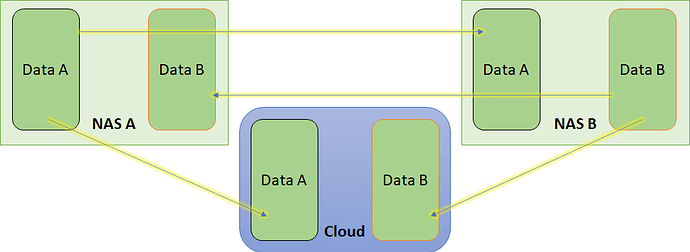
I’m spending some time thinking how I can introduce Cryptomator safely in my relatively basic NAS based environment. I have 2x NASes in 2x different sites that are running within a VM (debian/OpenMediaVault) and have been serving me for years. They copy/replicate each other overnight via rsync scripts.
Now, as I would like to encrypt my data I have initially thought about encrypting the NAS filesystem using LUKS but that doesn’t work the way I expect e.g. I need to unlock the volume manually (or automatically via some indirect procedure) after each reboot and still if I move off any file e.g. backup toward the cloud, content would be be unencrypted any ways.
So thank you for developing Cryptomator! 
What I am planning to do is:
- Keep my NASes
- Crate 1x vault per each site (since they both have the own content)
- For each NAS move all the data to the local vault
- Keep my rsync scripts solution to backup the cryptomator encrypted files
- On each NAS use rClone to upload the Cryptomator files onto pCloud
- Each LAN client will of course need to have Cryptomator installed and the vaults mounted
Now a couple of questions:
- Do you foreseen any issue with the above scenario?
- If a given vault is mounted (by multiple clients) can it be safely backed up? Or does the vault need to be unlocked to be backed up properly?
- I have some data that is to be accessed by the NAS itself e.g. movies to be served via Plex, I was never successful setting up Cryptomator-cli :-/ I’m also reading cli is released “in developement” so I guess unstable. Is there an alternative for the NAS to access the vault files via command line?
- Is there any way to store the password to unlock password/key (for Cryptomato-cli) on an external webserver? This would protect me further in case the NAS is physically stolen
Thanks!