Right now, Cryptomator for Android doesn’t provide a mount point to the user. This will change as soon as #35 is implemented but for now, it isn’t possible to open a file in another app and automatically keep this file in sync with the cloud. Currently you have to upload this edited file again using Cryptomator for Android and replace the origin file.
If you open a file with an external app like Keepass, we share this file using a ContentProvider with the other application. Before, we downloaded, decrypted and saved this file as temporary file to the internal storage of Cryptomator for Android on which only this app has access (/data/data/org.cryptomator/cache/decrypted/). After that, we share this file (only!) with the selected app, using a ContentProvider and only in read mode. The other application has only read access to the file and can not modify it. This will change as soon as #15 is implemented.
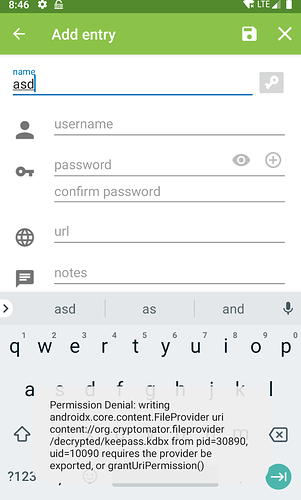
This is reproducable with a lot of apps also using Keepass: open a vault, select the keepass file, open it, change something and press save:
That means, Kepass has indeed no write permission to this file. Other apps often inform you before pressing save, that the file is only readable and can not be changed. Only creating a copy, changing the content and uploading again is possible until the two features mentioned above aren’t implemented.
The problem is, until now, we are not able to know, when the other app finished reading this file because of that, we are not able to delete the shared file as soon as it isn’t used anymore. Because of that, we implemented a workaround to clear the complete internal cache folder every 5 hours.
To summarize: If a file is shared with another app, we create a decrypted copy in internal, protected, app specific storage, share this file in read only mode and after max 5 hours, this decrypted file is removed.
@lockbot are you sure that you not used the export function, stored the file on the device and made changes in this file?