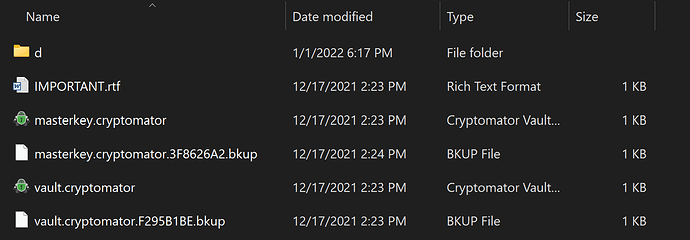
I do a weekly system image backup and also an additional backup of my Local vault (runs when its decrypted). Is there any need for the vault backup, or is this redundant with the system image backup and if so, where do I look to confirm it’s there? I am aware that the vault needs to be “unlocked and revealed” when either backup runs. When I open the system image backup, I do see a folder titled “Local Vault” under: PC > Windows > User > [Name] > Local Vault, and it contains all the expected Cryptomator files (vault, masterkey, backup, folder with all the encrypted content), but I think I was expecting to see all the decrypted folders and files.
encrypted cryptomator vault files are just files like any other.
So if your system image backup includes your whole hard drive, then yes, your vault is included.
(as you already mentioned)
no, because they are encrypted. What you see when you unlock a vault is a virtual drive and an unencrypted state of your encrypted files. But physically the files are still encrypted on your hard drive.
Nevertheless I recommend to have at least one backup that does not include cryptomator. Just in case something really bad happens to your vault.
OK, but there’s an interesting difference between the two backups…my hard drive image backup shows the vault contents in the encrypted state (as shown in the screenshot above). BUT my vault backup shows all my folders and files in an unencrypted state. They both backup using the same program, so why would the image backup show encrypted stuff and the vault backup shows everything unencrypted?
I can only assume as I do not know your exact backup setup.
But to me it looks like that your vault backup has the virtual drive as source and somewhere else as target. And then the unencrypted files from within the vault are backed up.
The system backup has your C partition as source (and thus your encrypted vault files) and so the encrypted files are backed up.
Yes, the vault backup points directly (and only) to my decrypted vault as the source and an external drive as the target.
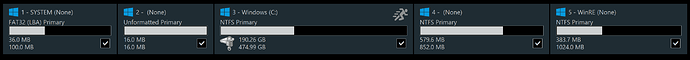
The system image backup includes all 5 partitions as shown below:
So this explains the difference between the two backups? And back to my original question, is it unnecessary to do the vault backup or does that serve the purpose (suggestion you made) about having a non-Cryptomator backup (technically it IS backing up FROM Cryptomator but in a decrypted form)?
yes
No, its not. Think about the following scenario:
For whatever reason one or more files in your vault was destroyed/corrupted by a malfunction of cryptomator, without you noticing it. Then none of your backups brings back your file. The system backups contain the encrypted state of your destroyed//corrupted file, the unencrypted backup is also a corrupted file, because it was taken out of a cryptomator vault. And as you didnt notice, maybe your historical files are also not usable anymore.
This is why I recommend to do at least 1 backup of a file, that does not need to have an other program (cryptomator or any other encryption software) to be accessed.
Please keep in mind: this is a very personal opinion and I might be a little paranoid when it comes to data security (but I never lost a file in decades).
Michael
Allow me to follow up on this as I was asked by someone and wasn’t sure of the correct response.
Since folders and files are placed in cloud storage (google drive, sync.com, dropbox), does using Cryptomator serve as a backup in case the laptop is destroyed or stolen? Meaning if the person gets a new laptop, installs CM and point to the masterkey file in the cloud, wouldn’t all the contents still be available?
Yes of course. You can add your online stored vault to any other cryptomator instance. In your case a new laptop.
So in that case, if all my physical files are on my laptop, but then my laptop is stolen, and I get a new one and reinstall CM and retrieve my files, didn’t that basically serve as a backup? That the files are in fact also stored in the cloud just encrypted?
btw - I still cannot get my backup software to “see” my vaults like before. Macrium staff looked over everything and said:
"Macrium Reflect requires you to open the software as an administrator to run. I suspect the mount point provided by Cryptomator may not be elevated which may be preventing Reflect from seeing these vaults.
Do you know how to configure CM to fix this? I used to be able to backup my vaults but cannot now since upgrading and switching to WinFsp configuration (I was using WebDAV but everuthing on the site suggested this is not optimal) - something broke and I cannot figure out what to do to get it back.
UPDATE:
I think I figured out how this all works (including backing up)…
- I select WinFsp (Local Drive) as my volume type
- “Use chosen directory” as my mount point
- I specify the path to the empty folder I create for that drive (in this case Windows (C:)>Users>william>Dropbox Mount)
- Restart CM for changes to take effect
- Unlock that drive in CM, and all my files encrypted files will be decrypted and accessible (in that folder)
- When I re-lock that drive, I can see in Windows Explorer that the files “vanish” and the folder appears empty when I refresh Explorer
I tested these steps and it seems this is how it is supposed to work, then, as far as backing up"
7. I configure Macrium Reflect to backup that same “Dropbox Mount” folder (when its decrypted of course)
8. I tested and it created a backup file
Do I finally have it right?? ![]()
Yes. But it’s basic recommendation to have more than one backup in your backup strategy. And I personally recommend to have at least one unencrypted (of course not online but in a save local place)
Agreed. I will have them on my external drive protected with Bitlocker
Also I just added what I hope is the solution to my backup issue…would love to know if it is correct!!
Nothing wrong here from my point of view
Hello,
I hope it is okay to post in this old topic, but I have the same problems as @Blue_Sky before.
Backup software (Veeam, Macrium, AOMEI) is unable to back up my vault.
Even when I use WinFSP (local drive) and a mount point in a folder, the software tells me, the file system was not recognized (Veeam) or the mount point is untrustworthy (Macrium).
I read, there could be problems with admin rights, but I thought, I could bypass this, using a folder as mounting point?
SyncBackSE as non elevated software is able to look into the folders.
Do you have an idea, what is wrong with my settings?
I am using the latest WinFSP (from their website) and latest cryptomator on Windows 11.
Thank you very much.
Edit: so it is the same question, posted here:
How to fix this now?