Not sure of the best way to do this. If you create a vault on your local hard drive, will it be included in scheduled backups to an external drive using a program like Aomei Backupper, Macrium Reflect or EaseUS Todo?
Depends on how you have configured your backup. At the end, the encrypted vault files are just normal files like any other of your files. Nevertheless I always recommend to have at least one backup of your files that is not encrypted. So you can restore it without the need to use additional software like Cryptomator.
(Think of a situation where your vault is damaged for whatever reason. Then it’s good to have a backup of the files that were in the vault)
If a file/folder contains sensitive/confidential information to justify encrypting it, why would you run the risk of keeping an unencrypted copy of it (anywhere)? I suppose you could store a version in the cloud encrypted via Cryptomator, and another copy on a local or external drive and encrypt that with Veracrypt. Just seems like you’re inviting confusion over version control if you make changes to anything. But storing an unencrypted copy seems like playing with fire.
Ideally, I’d like as few steps as possible, so something like 1) create a vault with CM and dump all confidential folders and files into it. 2) Open that vault whenever you want to make any changes to anything it contains. 3) Scheduled backups include that vault, so now you have an encrypted copy of that vault on say, an external drive, and 4) the vault also syncs to a cloud platform, so now you also have an encrypted, off-site copy in case your house burns down. BUT…you only need to make changes/maintain the original vault, and anything done there is mirrored in your local backup and your online “backup.” Double redundancy - full synced.
Let me know if you think this works:
- Sync.com client creates a local folder “Sync” which seems similar to a Google Drive or Dropbox syncing folder
- I created multiple vaults within that Sync folder
- I can add/delete/modify files in these vaults just like normal when mounted, and any changes reflected when it syncs to the cloud
- Then…I configured my backup software to include that Sync folder (along with the usual stuff like Documents, Photos, Desktop, etc.), so that should now be backed up to my external (backup) drive (it does an incremental back up every 24 hrs.)
- So in the end…I use CM like normal, but I have “dual-redundancy” in that the folder with my vaults (Sync folder) is A) backed up to my external drive, and B) sync’s to the cloud.
Thoughts?
Backups are to avoid loss of data. Encryption is to keep privacy. No need to encrypt something when it is stored at a place where it is private (and that’s where a „clean“ backup should be stored). Of course I do have backups online (my house can burn as well) and of course they are encrypted with Cryptomator. But my main backup is unencrypted („untouched“) and in a local safe (yes, I have multiple backups). I just don’t like the thought of relying on an additional software just to restore a file from my backup. What if the vault is corrupted? What if your backup veracrypt container is faulty? (personal thing, there are other opinions for sure)
It depends where you store it ![]()
Technically looks good to me.
But I can’t say anything about sync.com as I do not use it. Maybe someone else?
The thing is, I keep my backup (external) drive connected to my laptop pretty much 24/7, since it is on a backup schedule once a day. Just easier than finding it and connecting it / disconnecting it all the time. That said, if I simply backup an unencrypted copy and somehow the laptop and drive were stolen, they perpetrator would have easy access to the unencrypted stuff.
I suffered an external drive failure this past year. I was stupid and had a lot of stuff on the external drive that was the only version (no backup), so when the drive died, all that was lost. The new process is to use that drive exclusively for backup purposes.Thats only part of a two-part solution, because I also keep encrypted copies of really important stuff in the cloud, in case of fire or theft, in which case both the laptop AND external drive would be gone.
If your main point is that Cryptomator could fail and the vaults would be useless, I guess that could happen. If that’s the case, I could keep a “duplicate set” of everything I have in Cryptomator in a Veracrypt vault (completely separate from anything Cryptomator does). I think the likelihood of BOTH failing is astronomically low. Just more of a hassle to maintain two distinct vaults. But back to your original point, to me anyway, keeping an unencrypted copy of anything you feel is confidential enough to warrant putting it in a vault (any kind of vault) seems to run counter to your mission and begs the question why encrypt them in the first place? Under that logic, you would keep a written log of all your logons and passwords to every account you have in case your password manager tool fails.
Because I store them online
Correct. That’s why I just „know“ the logins for crucial accounts (in addition to the password manager). In addition: every service offers a „account/password“ lost process.
Let’s agree we just disagree on how we use encryption tools and backup tools. ![]()
As I said, it’s just a personal thing and just gave a recommendation. No need to follow it if you do not feel comfortable with it.
Michael - I wanted to revisit this briefly. I have a vault that is synced to a cloud storage service (sync.com). Each morning I open Cryptomator and unlock the vault. At the end of the day I re-lock the vault (no longer visible in File Explorer). Are the encrypted files stored locally on my laptop, or are they encrypted in the cloud via Sync.com? Suppose there is a fire and my laptop is destroyed. Once replaced, and after I reinstall CR and point it to my Sync.com account, will all the folders and files be accessible again? I know CR isn’t intended as a backup tool, but since thats how I access these files, and since without it the stuff sitting out on Sync. com is just the masterkey and vault (and everything shows as just 1KB), 'm still trying to wrap my head around where they “physical” manifestations of the files are located.
You write
So I Wonder why you ask if the files are encrypted locally or in the cloud? It’s both if the local (encrypted) vault files are synced with your cloud storage.
So if you have a new pc, just sync your (encrypted) vault files from your cloud storage to your local drive, and add the vault to the Cryptomator app.
Ps: if all your encrypted vault files online just have 1kb, then you should check the sync or check the file size via browser direct online. Unless you do not have only 1kb files in your vault, there is something going wrong with the sync.
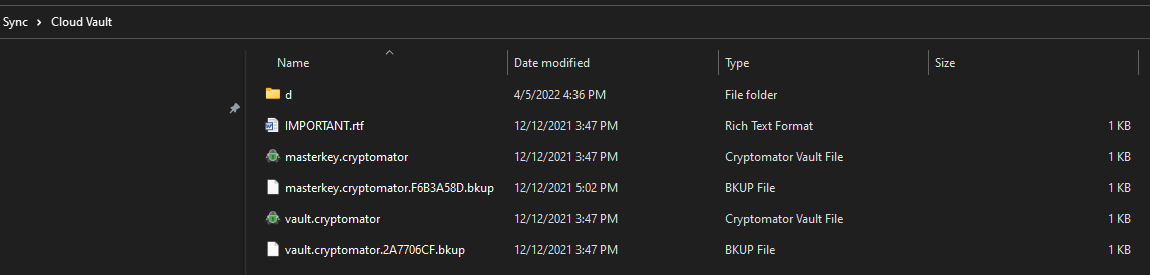
Here is what is in Sync.com. However, in the “decrypted state” as seen via File Explorer, my vault has 30 item totaling 188 GB.
It seems to be working correctly. I just created a second test vault, told it to store the encrypted files in the same folder as the first vault (the Sync folder on my laptop (works just like Onedrive or Dropbox in putting a folder on your machine), and added a file. Everything appears the same as the first vault (all the same masterkey and vault files as the first one; all showing 1 KB)
Yea, well. The masterkey/vault files actually do have only 1 kb.  . I thought you are talking about all the files in „d“
. I thought you are talking about all the files in „d“
The files in „d“ should be round about the size of your unencrypted files. As this seems to be the case, everything looks good so far.
Yes, “d” has quite a few folders (although it impossible to see if they match up. “d” has many more individual folders listed whereas my vault has many folders “nested” inside other folders)
OK, so bottom line is, if my laptop gets stolen, burns up, etc., Once i replace the machine, install Cryptomator and download whats sitting out on Sync., I should be back in business right?
Yes that’s right. Nevertheless I recommend 3-2-1 backup strategy and not rely only on that one online backup. (If your interested you’ll find lots of info about this if you google „3-2-1 backup“)
I have a second backup - an external drive that backs up the decrypted vault at regular intervals. Actually, it may even count as two because one backup is the vault specifically, and another routine backup is an entire system image backup (which should by default also include the decrypted vault)